Do you really need full cybersecurity coverage? Can't your users make do with the current state of your identity management platforms, even if they have a few hiccups? If that is...
Resources & Downloads
Check out our latest analyst reports, datasheets, events etc.
Infographics
All – Case Studies – Datasheets – E-Books – Infographics – Reports – White Papers
Infographic – Fulfill your Benchmarking Objectives with Identity Orchestration
Once your maturity benchmarking session is done, you need to move on to implementation of the lessons learned. Perhaps your internal team might attempt the herculean task of...
Infographic – What Sets A Simeio Benchmark Apart?
CISOs and C-Suite executives are starting to recognize the crucial role identity plays in their operations. Consequently, IAM maturity has emerged as the key metric for judging...
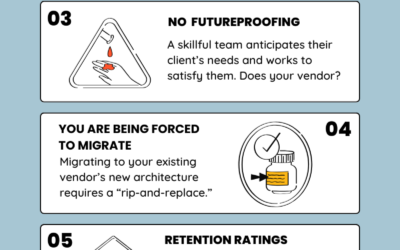
Infographic: 7 Symptoms it’s Time to Switch your Identity Management Vendor
One of the most difficult challenges facing CISOs and company stakeholders is the difficulty of transitioning out from a sub-par identity management vendor. Such a move can be...
Infographic: 5 Keys to Addressing Privileged Access
Addressing privileged access is one of the key requirements of a mature identity fabric. A strong privileged access solution enables swift remediation of emergent security risks....
Infographic – The Simeio IAM Maturity Improvement Journey
IAM maturity improvement requires a solid foundation, a decisive execution, and a reliable plan for future development. Many enterprises are beginning to realize the importance...
Infographic – Balancing Efficiency in Mature IAM Programs
Balancing productivity with security is one of the longstanding challenges of effective identity management, and the hallmark of mature IAM programs. But, by adhering to these...
Infographic – Top 3 Features of Mature IAM Programs
Achieving mature identity management is an uphill battle that requires careful planning and execution. However, though the process is complex, the benefits of stronger...
Infographic – Application Recertification Checklist
Application recertification within an updated identity platform can be one of the most arduous and costly stages of the application onboarding process. Fortunately, by adhering...
Infographic – Top 5 SKO Insights: Identity Management Priorities
The proper ordering of identity management priorities is crucial for anyone involved in the identity management. Top decision-makers come to Simeio for insights into the best...
Infographic – 5 Reasons Why Identity Orchestration is Key to a Robust IAM Program
Identity orchestration manages and coordinates an organization’s various identity-related processes and systems. By integrating different identity management technologies, such...
Infographic – 7 Symptoms that it’s Time to Ditch Your Identity Vendor
Identity vendors must be regularly evaluated to ensure they are still worth the investment. If a vendor becomes more of a burden than an asset, why would you pay to stay...
Infographic – IAM in Healthcare
From patient portals to caregiver records, safeguarding and optimizing user data is a chief concern in modern healthcare. Learn how IAM in Healthcare contributes to a healthy...
Infographic – Managed IAM in Retail
Retail has gone heavily digital and that means identity (and its management) has become paramount to marketplace success. Managed IAM in retail contributes to smoother...
Infographic – Managed IAM in Finance
A smart investor knows how to maximize their returns. From compliance with critical identity regulations to building customer confidence, identity and access management (IAM)...
Infographic – Advantages of Identity Federation for Businesses & Users
How do you control your identities, their permissions, and the risks of both? You need identity federation to bring together all of your siloed identity components, providing a...
Infographic – Why CIEM Managed Services?
Are your cloud platforms as secure and efficient as they could be? Cloud Infrastructure Entitlement Management (CIEM) is a young aspect of Identity and Access Management (IAM)....
Infographic – How the 4 Pillars Contribute to Identity Maturity
Want to know the measure of your identity and access maturity? Start with the four pillars of AM, CIAM, IGA, and PAM.
Infographic – 8 Components of IAM Maturity Assessment
IAM Maturity is crucial to understanding the state of your Identity program, but what goes into it? Learn the 8 building blocks of a comprehensive and meaningful IAM Maturity...
Infographic – Managed IAM in Energy
IAM solutions and services can energize your energy enterprise. IAM in energy enterprises keeps the identities of customers, internal users, and even machines secure....
Infographic – Five 2023 IAM Trends Every CISO Must Focus On
In cybersecurity, anticipation and prevention are the core of effective cybersecurity. As bad actors constantly probe your perimeters for weaknesses, your enterprise must...
Infographic – The 6 Identity and Access Security Questions you Need to Answer
If you can't answer all 6 identity and access security questions at a moment's notice, your IAM security program is vulnerable! Learn why each question is important to your...
Infographic – The 10 Most Common Identity Management Mistakes
IAM Mistakes are expensive and far too common. But by familiarizing yourself with the most common identity mistakes you are most likely to make, you stand a much better chance of...
Infographic – 6 Telltales of a Vulnerable Identity System
How can you tell if you have a vulnerable identity system? For a start, if you answer yes to any one of these 6 vital identity security questions, take immediate action. Your...